This is an old revision of the document!
Table of Contents
SurePet Feeder
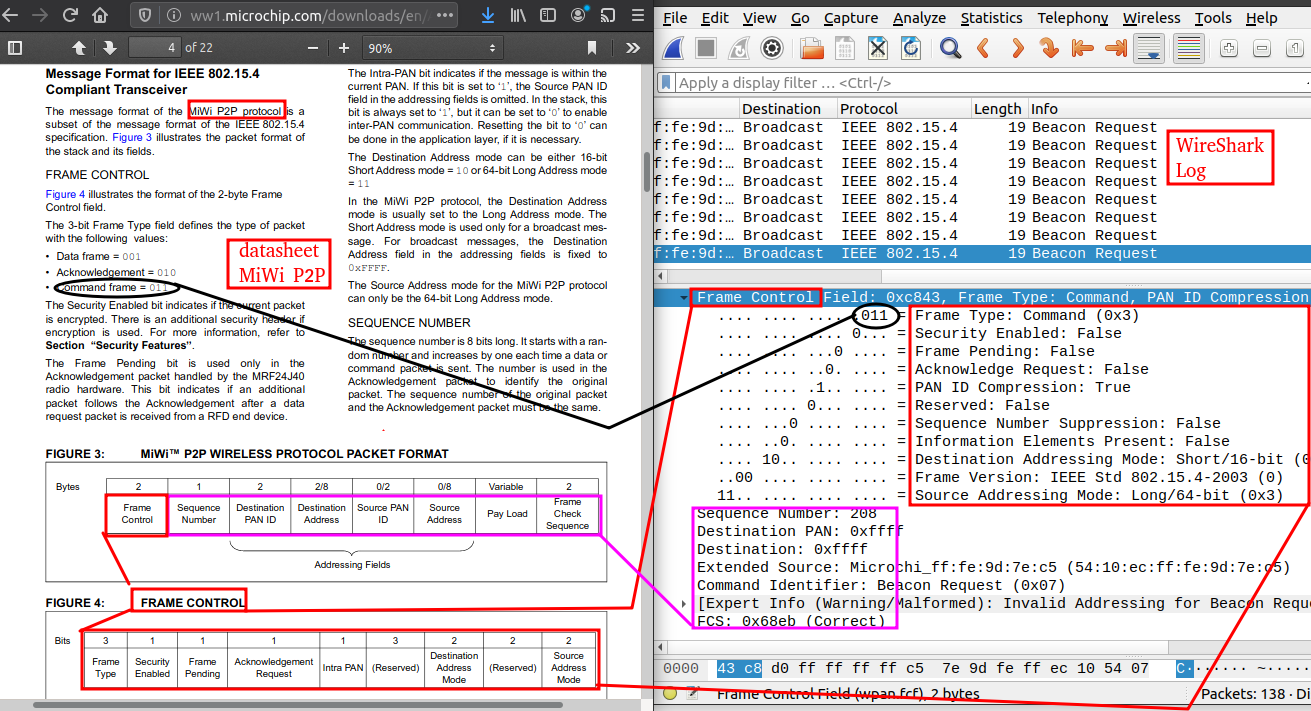
The SurePet Feeder uses a 802.15.4 based protocol called MiWi P2P. This is a protocol that is made by Microchip.
Research
The following link shows someone who has captured some of the P2P frames and has mapped them to a spec:
https://github.com/alextoft/sureflap/issues/8#issuecomment-698580972
From the following link, it appears that the beacon is transmitted on channel 15:
https://github.com/Koenkk/zigbee2mqtt/issues/3261#issue-591745054
The best link so fare is:
Protocol Sniff
Ideally we would use the Zena sniffer, however I seem to of bricked it.
The Zena software allows for protocol decode of the MiWi P2P protocol.
So instead for now we are using a UZBee+.
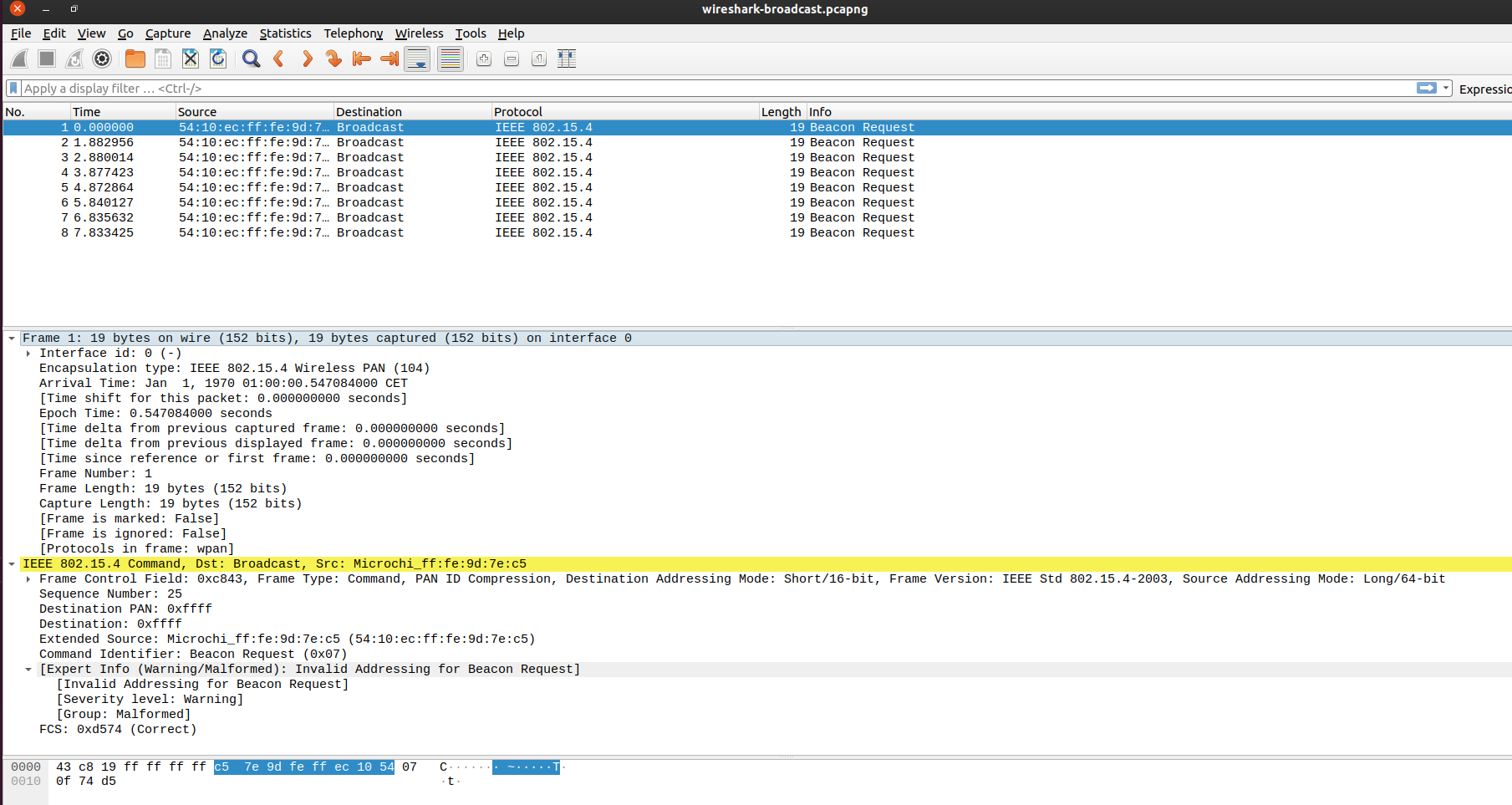
After creating a simple sniffer tool, when the “setup” button on the SurePet device is pressed, the following packet is received:
b'+PDAI=1343C832FFFFFFFF6E2A02C0F9D5B370072FECE8\r\n'
The MAC address is printed on the bottom of the device, This matches the above packet.
1343C832FFFFFFFF6E2A02C0F9D5B370072FECE8
13=Length
So
43C832FFFFFFFF6E2A02C0F9D5B370072FECE8
6E2A02C0F9D5B370=Mac (reversed)
The P2P protocol is documented in the following document:
https://ww1.microchip.com/downloads/en/DeviceDoc/00001204C.pdf
So the full payload decodes as:
- 43C8=Frame Control
- 32=Sequence Number
- FFFF=Destination PAN ID
- FFFF=Destination Address
- Source PAN ID (0 bytes)
- 6E2A02C0F9D5B370=Source Address
- 072F=Payload
- ECE8=Frame Check
And the Frame Control:
43C8=
Test 1:
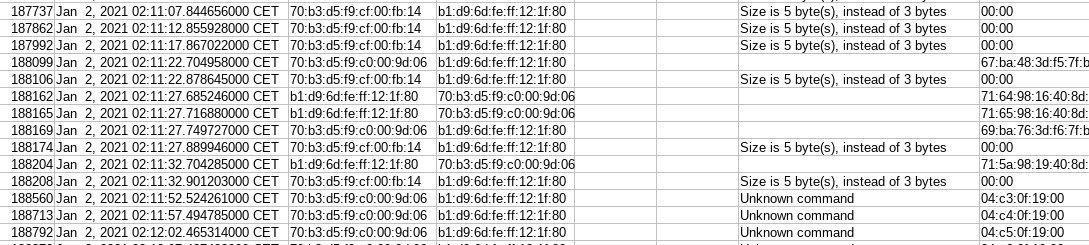
16
CC01 00 FFFF 70B3D5F9C0022A6E 70B3D5F9C0022AD4BE
- CC01=Frame Control
- 00=Sequence Number
- FFFF=Destination PAN ID
- 70B3D5F9C0022A6E=Destination Address
- Source PAN ID (0 bytes)
- 70B3D5F9C0022AD4=Source Address
- 072F=Payload
- ECE8=Frame Check