Table of Contents
NHS Contact Tracing App
The NHS contact tracing app uses Bluetooth Low Energy to transmit a unique ID, this ID is changed at a periodic interval. This topic details questions about how this process works with the intention to find answers.
How is the unique ID generated
There are two main options, the first is a seed that is “spun” to generate the next value. Or a pure random value that is created each time. Both methods have there advantages and disadvantages, for example using a Seed means that the app only needs to store the seed and can calculate the values sent within a day easily, this means less storage is needed to store all the values, however leaking the seed allows an attacker to re-generate all the values the app generates for a given time.
From https://www.ncsc.gov.uk/blog-post/security-behind-nhs-contact-tracing-app
It looks like a seed is used.
“Every day, your device generates a random elliptic curve key pair and encrypts your installation ID (and some other administrative stuff like time periods) with it in a way that only the NHS server can recover, ”
How often is the Unique ID changed
To prevent tracking a user through space, the Unique ID is changed, how often effects the exposure. For example if its changed on every transmission, then it becomes very difficult for the samples points to be “joined” together, however if its only changed once every 10 minutes, it means it can be used to track around shops or along roads.
Does The contact app exchange values
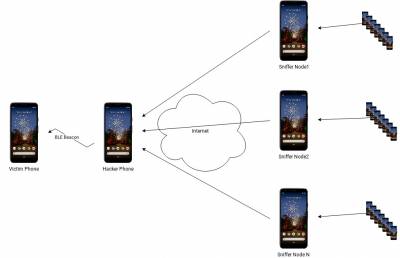
This is a very important question. If the app just records the beacons it sees without performing any additional authentication, then the app is open to a BLE proxy attack.
This attack can be simplified if the attacker has access to a known “infected” source. This means that an attacker could distribute an infection event to a larger number of victims. This would generate false positive results to the victims.